我正在尝试通过 Azure AD 应用程序角色创建一个 protected Controller 。
这里是 Startup.Auth 的豁免,基本上由 Visual Studio 模板提供:
public void ConfigureAuth(IAppBuilder app)
{
ApplicationDbContext db = new ApplicationDbContext();
app.SetDefaultSignInAsAuthenticationType(CookieAuthenticationDefaults.AuthenticationType);
app.UseCookieAuthentication(new CookieAuthenticationOptions());
app.UseOpenIdConnectAuthentication(
new OpenIdConnectAuthenticationOptions
{
ClientId = clientId,
Authority = Authority,
PostLogoutRedirectUri = postLogoutRedirectUri,
Notifications = new OpenIdConnectAuthenticationNotifications()
{
// If there is a code in the OpenID Connect response, redeem it for an access token and refresh token, and store those away.
AuthorizationCodeReceived = (context) =>
{
var code = context.Code;
ClientCredential credential = new ClientCredential(clientId, appKey);
string signedInUserID = context.AuthenticationTicket.Identity.FindFirst(ClaimTypes.NameIdentifier).Value;
AuthenticationContext authContext = new AuthenticationContext(Authority, new ADALTokenCache(signedInUserID));
AuthenticationResult result = authContext.AcquireTokenByAuthorizationCode(
code, new Uri(HttpContext.Current.Request.Url.GetLeftPart(UriPartial.Path)), credential, graphResourceId);
return Task.FromResult(0);
}
}
});
}
尝试过具有如下属性的 ApiController:
[Authorize(Roles = "Administrators")]
// GET: api/Questions
[ResponseType(typeof(Question))]
public IHttpActionResult GetQuestions()
{
....
}
和一个 MVC Controller :
[Authorize(Roles = "Administrators")]
public ActionResult Index()
{
....
}
在 Azure 应用程序 list 中定义了以下内容:
"appRoles": [
{
"id": "B4531A9A-0DC8-4015-8CE5-CA1DA1D73754",
"allowedMemberTypes": ["User"],
"description": "Administrators",
"displayName": "Administrators",
"value": "Administrators",
"isEnabled": true,
"origin": "Application"
}
]
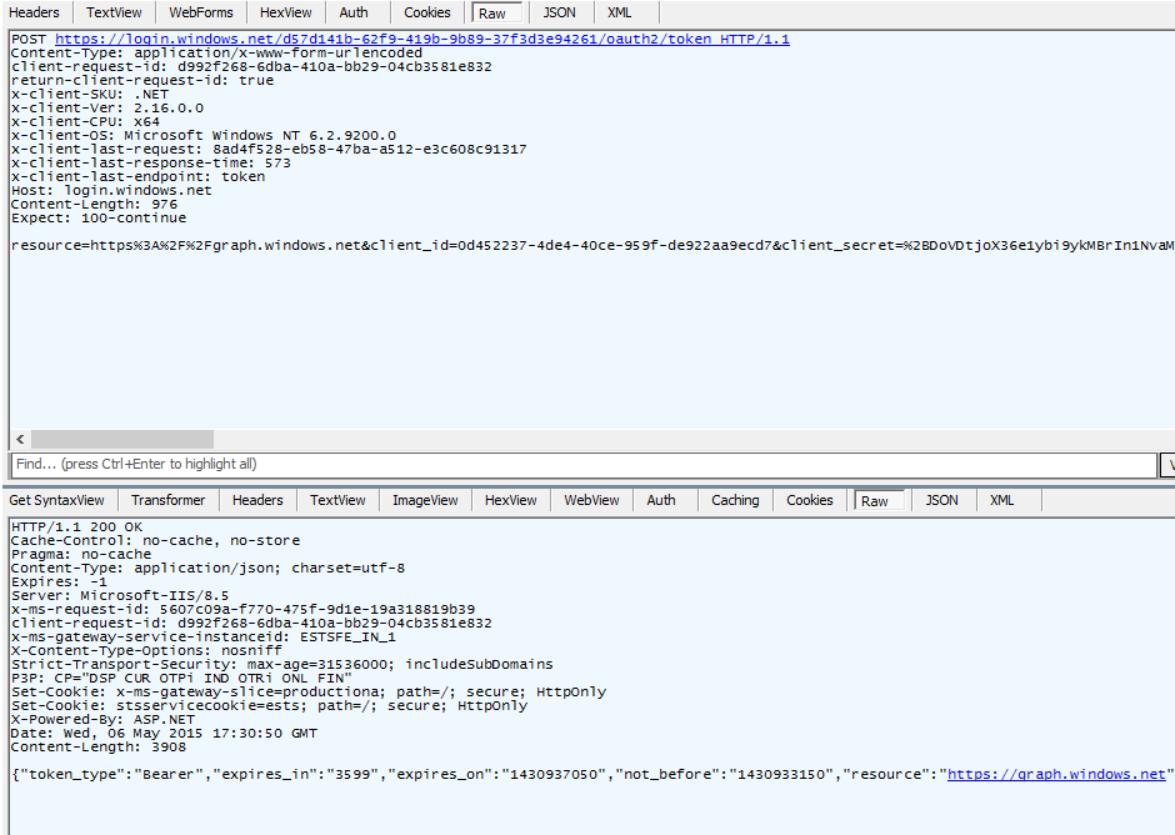
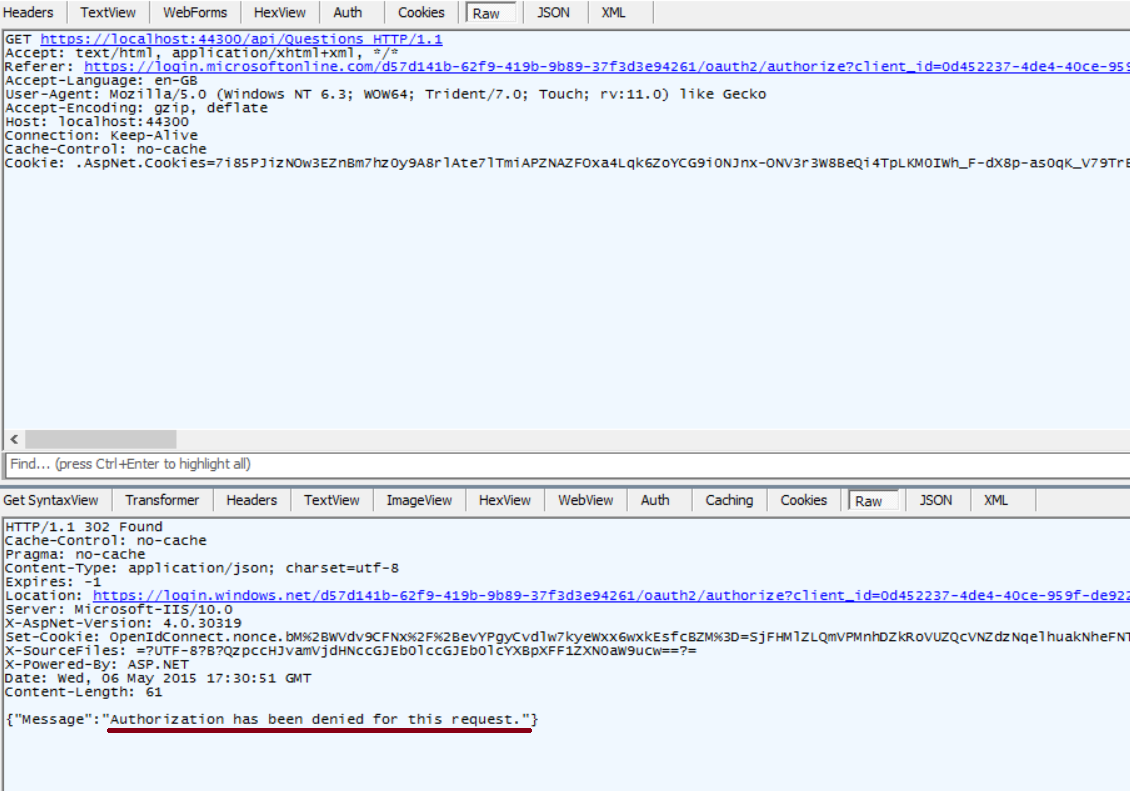
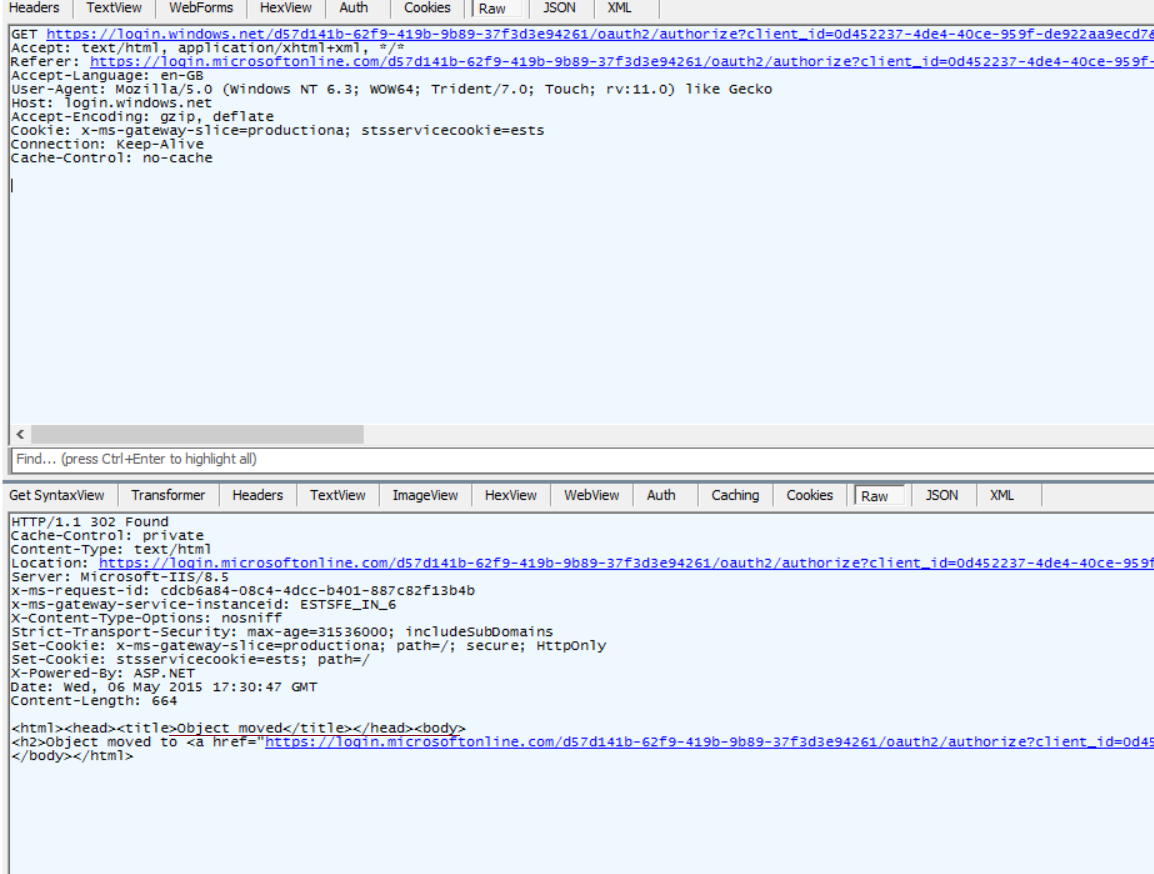
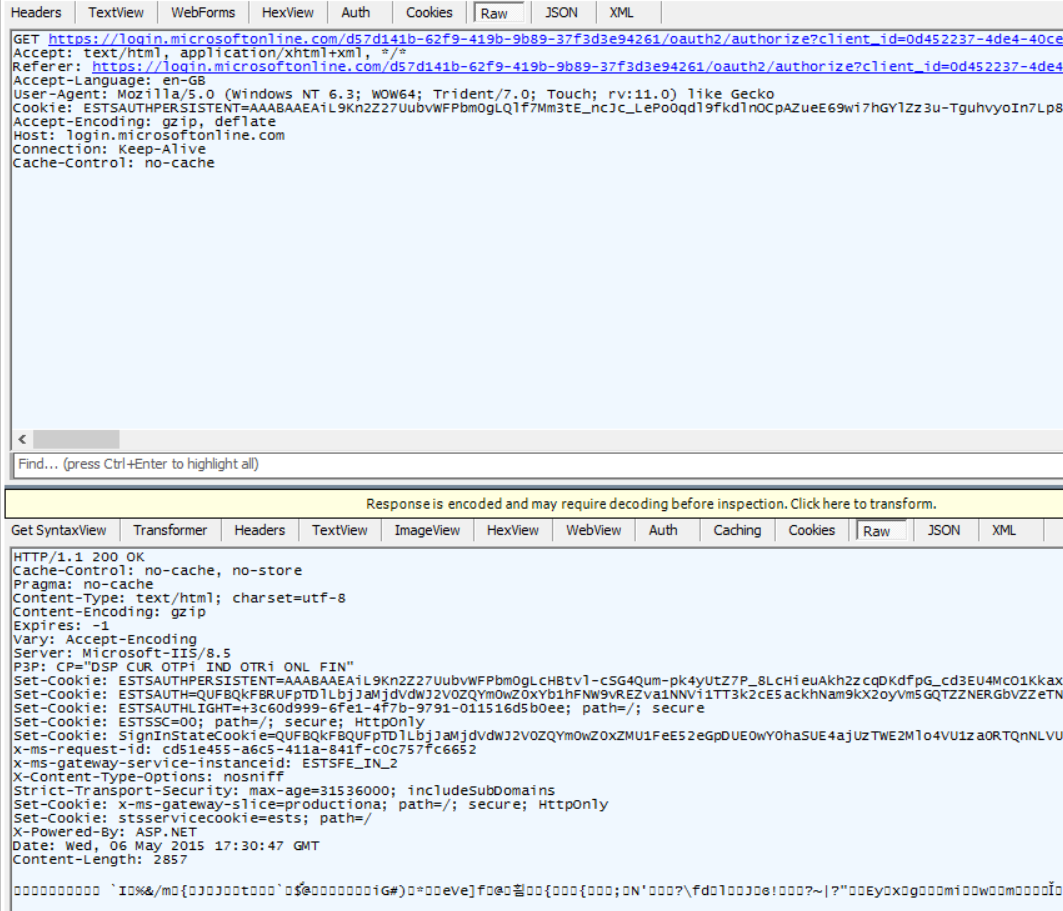
现在执行/api/Questions 的 GET 请求重定向到 https://login.microsoftonline.com并且用户身份验证似乎是成功的,此外本地主机和微软在线之间存在无限循环的请求。见下文:
我做错了什么?
使用 [Authorize] 效果很好。
最佳答案
事实证明,应将以下内容添加到 Startup.Auth:
TokenValidationParameters = new System.IdentityModel.Tokens.TokenValidationParameters
{
ValidateIssuer = true,
// map the claimsPrincipal's roles to the roles claim
RoleClaimType = "roles",
}
它实际上是在配置“角色”声明类型,以便将其映射到默认行为。 优秀的解释可在: https://samlman.wordpress.com/2015/03/09/using-roles-in-azure-applications/
关于asp.net-mvc - Azure AD 应用程序角色,我们在Stack Overflow上找到一个类似的问题: https://stackoverflow.com/questions/30084214/